Intigriti’s XSS Challenge (February 2024)
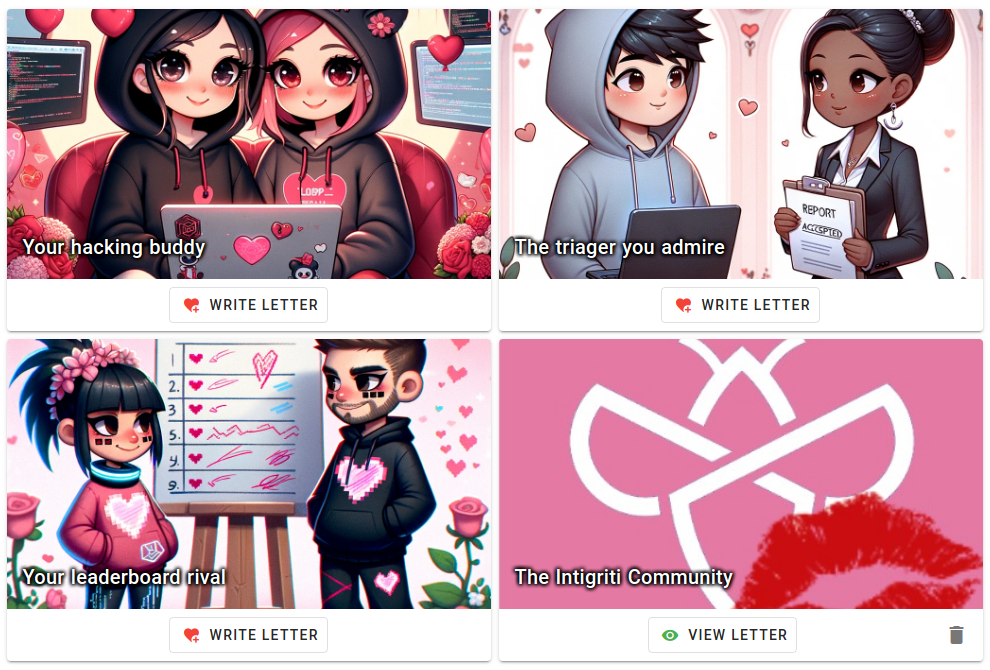
I came across with @intigriti’s XSS challenge this month. This time we are given a love letter storage system which allow us to show our love to our hacking buddies.
TetCTF 2024: adapt
Creating fake proofs on cosmos/iavl@v0.19.7
TetCTF comes back with their great crypto challenges. I played with @blackb6a and we ended up securing the 🥉 third place. In this blog post, I will walk through adapt, a challenge which required us to make fake proofs in an IAVL tree implementation. There are only three solves during the contest period.
HKCERT CTF 2023 Postmortem (III): The Remaining Challenges

We will finally cover the non-crypto challenges that I wrote for HKCERT CTF 2023. This includes one misc (Hackforces), two pwn (ISA Jump Scare & ISA Jogger) and two reverse (The Flag Game & Loot and Scoot) challenges.
HKCERT CTF 2023 Postmortem (II): Harder Crypto Challenges

In the second part of the series, I will cover four cryptography challenges: baDES, Maybe Someday, Cipher Bridging Service and RSA Triooo. Interestingly, most of them are somehow “plagiarized” from the other CTFs.
HKCERT CTF 2023 Postmortem (I): Easier Crypto Challenges

This is yet another moment that Black Bauhinia co-organizes HKCERT CTF. This year, I am slightly more productive than the previous years and wrote 13 challenges for the CTF. There are three blog posts in this series, where I will respectively cover the author’s solutions to the easier crypto challenges, the harder crypto challenges and the remaining challenges.