2024-06-24
:: Mystiz
#ctf
#google-ctf
#challenge-writing
Related key attack on reduced-round IDEA
IDEA is a challenge written by @0xdeuterium. He even provided me the paper to refer, my only contribution to the challenge is to optimize the original solution so that we don’t need 65K-ish oracle calls.
2024-06-24
:: Mystiz
#ctf
#google-ctf
#challenge-writing
MD5 in ZKP? YNGMI
ZKPOK is a challenge I made while learning Zero Knowledge Proofs on zk-learning.org. I was watching the first lecture video, I came across with the interactive proof for quadratic residues at 20:00. This made me ponder - it should be easy to apply Fiat-Shamir transform to make this non-interactive. Let’s also use MD5 so that it could be vulnerable. Hours later, this challenge appeared without a proper solve script.
2024-06-24
:: Mystiz
#ctf
#google-ctf
#challenge-writing
This is yet another edition of Google CTF, where I wrote some crypto challenges with my colleagues. I contributed on three challenges this time, namely, Blinders, ZKPOK and IDEA. There are respectively 56, 3 and 4 solves (out of 267 teams scoring non-zero flags) during the contest period.
Blinders is one of the challenges I coauthored, which introduces a protocol for private set membership.
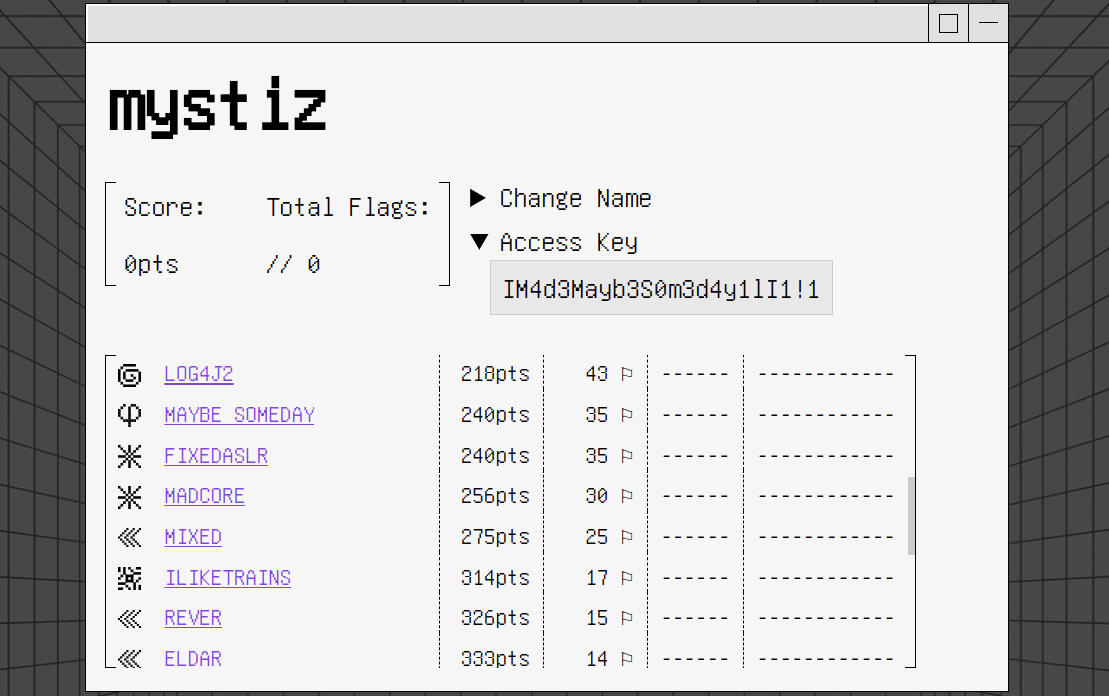
2024-01-27
:: Mystiz
#ctf
#hkcert-ctf
#challenge-writing
#reverse
#pwn
#misc

We will finally cover the non-crypto challenges that I wrote for HKCERT CTF 2023. This includes one misc (Hackforces), two pwn (ISA Jump Scare & ISA Jogger) and two reverse (The Flag Game & Loot and Scoot) challenges.
2024-01-27
:: Mystiz
#ctf
#hkcert-ctf
#challenge-writing
#crypto

In the second part of the series, I will cover four cryptography challenges: baDES, Maybe Someday, Cipher Bridging Service and RSA Triooo. Interestingly, most of them are somehow “plagiarized” from the other CTFs.
2024-01-27
:: Mystiz
#ctf
#hkcert-ctf
#challenge-writing
#crypto

This is yet another moment that Black Bauhinia co-organizes HKCERT CTF. This year, I am slightly more productive than the previous years and wrote 13 challenges for the CTF. There are three blog posts in this series, where I will respectively cover the author’s solutions to the easier crypto challenges, the harder crypto challenges and the remaining challenges.
2024-01-21
:: Mystiz
#ctf
#firebird-training
#challenge-writing
#crypto
This is yet another annual Firebird CTF and I only wrote one cryptography challenge this time, Goldilocks. There were one solve (out of 53 participating teams) during the contest period.
2023-08-21
:: Mystiz
#ctf
#b6actf
#crypto
#challenge-writing
After four years of team formation, we organized our first edition of Bauhinia CTF last weekend. There are over 650 teams registered and over 200 teams scored. This year, I made one crypto challenge, How to Stop Time. I also coauthored a web/crypto challenge, Amnesia, with @chthollic_.
This post is served as a short writeup of How to Stop Time, a crypto challenge with six solves during the contest period.
2023-06-26
:: Mystiz
#ctf
#google-ctf
#crypto
#knapsack
#challenge-writing
MHK2 is one of the challenges I coauthored for Google CTF 2023 and there were 18 teams solving this challenge during the contest time.
2023-03-06
:: Mystiz
#ctf
#mocsctf
#challenge-writing

I prepared three challenges on behalf of @blackb6a for MOCSCTF, which is a 8-hour long CTF happened yesterday. This blogpost serves as the write-up for the three challenges that I wrote.
There are two solves (out of 40 participants) for Three-pass, and zero solves for jav-asr-ipt and Catch-22 Mini.
2023-01-30
:: Mystiz
#ctf
#firebird-training
#challenge-writing
#crypto
Like in 2021 and 2022, I contributed some challenges for Firebird’s internal CTF, which are from the Hong Kong University of Science and Technology. This time I wrote three crypto challenges: Randomsum, Shelter and Threerider.
There were 24 teams participating. There were three solves for Randomsum, while Shelter and Threerider were unsolved during the CTF.
2022-12-24
:: Mystiz
#ctf
#hkcert-ctf
#challenge-writing
#reverse
#minecraft

In the last part, I will include the two non-crypto challenges I wrote for HKCERT CTF 2022: Numbers go brrr and Minecraft geoguessr.
2022-12-24
:: Mystiz
#ctf
#hkcert-ctf
#challenge-writing
#crypto

We will continue walking through the remaining crypto challenges I wrote for HKCERT CTF 2022: Mystiz can’t code, Slow keystream and King of Rock, Paper, Scissors.
2022-12-24
:: Mystiz
#ctf
#hkcert-ctf
#challenge-writing
#crypto
This is the third year Black Bauhinia co-organized HKCERT CTF. This time I wrote nine challenges: Seven crypto, one reverse and one misc.
Similar to the last year, I have a series of three blog posts walking through the challenges that I wrote. We will discuss the four easier crypto challenges: Flawed ElGamal, Catch-22, Rogue Secret Assistant and Base64 encryption.
2022-10-19
:: Mystiz
#ctf
#google-ctf
#challenge-writing
#crypto
#rsa
#bleichenbacher
Bleichenbacher strikes back again (and again)
HACKING GOOGLE is a documentary of Google’s cybersecurity teams and H4CK1NG G00GL3 is it’s CTF counterpart. Project Zero Adventure is a cryptography challenge I wrote.
In the game, the players control the Security Princess to dodge the obstacles and catch the bugs (a variant of Google Chrome’s dinosaur game). After that, the server will sign messages consisting of the players' name and the score via the /sign API. The players will then submit it to the /highscore API. If the score submitted to the highscore API is negative, they will be given the flag.
However, there is one catch: The server is only willing to sign the results with non-negative scores.
2022-07-20
:: Mystiz
#ctf
#google-ctf
#challenge-writing
#crypto
#paillier
This is the third year I had a writeup on Google CTF (see my writeup in 2020 and 2021). Yet this time it is the official writeup for a challenge - as the challenge author! There are eventually 35 solvers (out of 382 teams) for the challenge.
2022-02-19
:: Mystiz
#ctf
#mocsctf
#challenge-writing
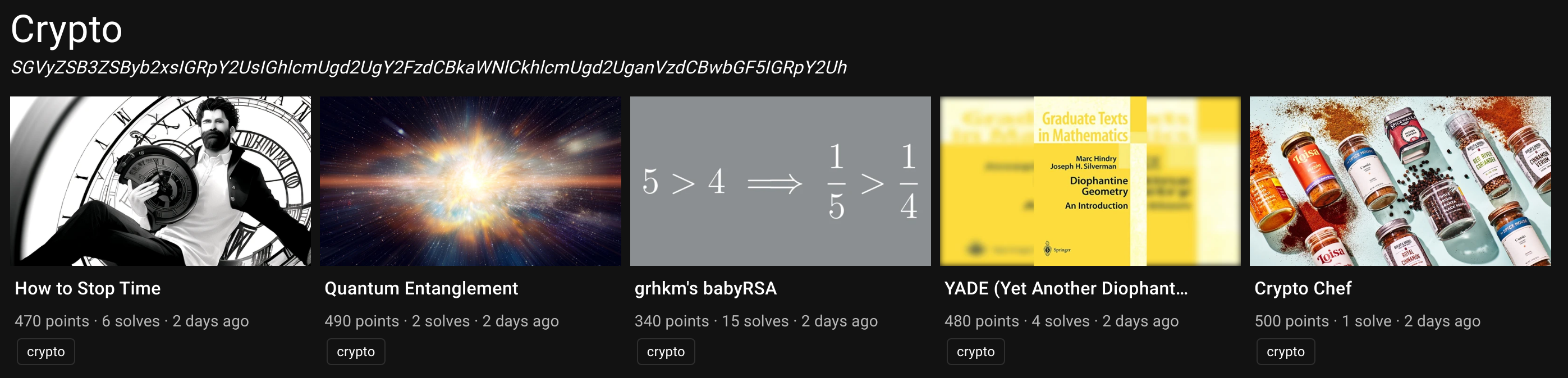
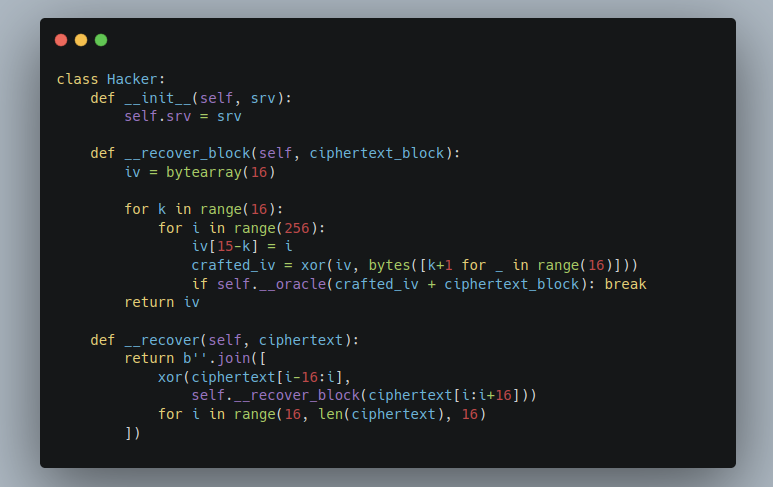
@blackb6a helped preparing some challenges for MOCSCTF, a 8.5-hour long CTF in Macau. This time I wrote nine challenges and @hoifanrd made one of them (3-AES). This blog post covers the intended solution for all of them.
2022-01-23
:: Mystiz
#ctf
#firebird-training
#crypto
#challenge-writing
This is the time that Firebird Internal CTF happens. I made three crypto challenges this year - Lack of Entropy (⭐), Authenticator (⭐⭐) and Collider (⭐⭐). I will discuss the solution for all of them in the blog post.
2021-11-18
:: Mystiz
#ctf
#hkcert-ctf
#challenge-writing
#web
#pwn
#algorithms
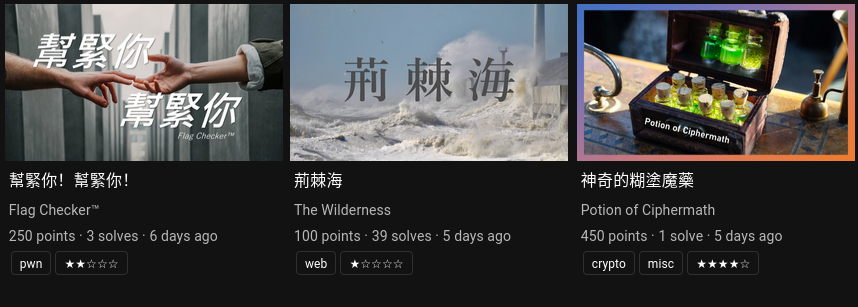
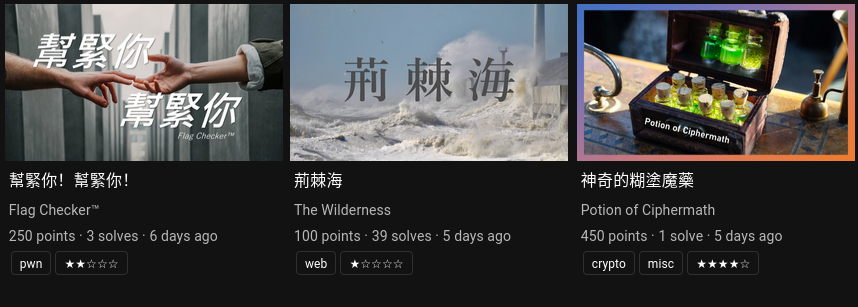
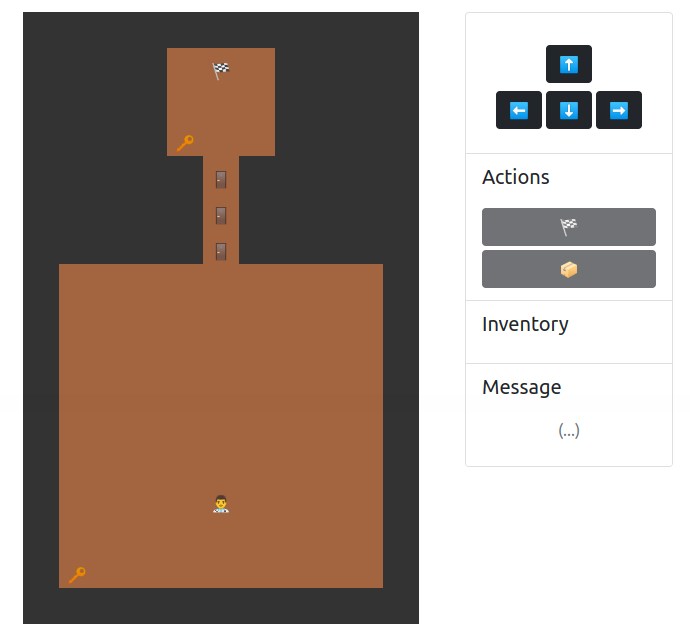
We will cover the remaining challenges I wrote in this part: Flag Checker™, The Wilderness and Potion of Ciphermath.
2021-11-18
:: Mystiz
#ctf
#hkcert-ctf
#challenge-writing
#reverse
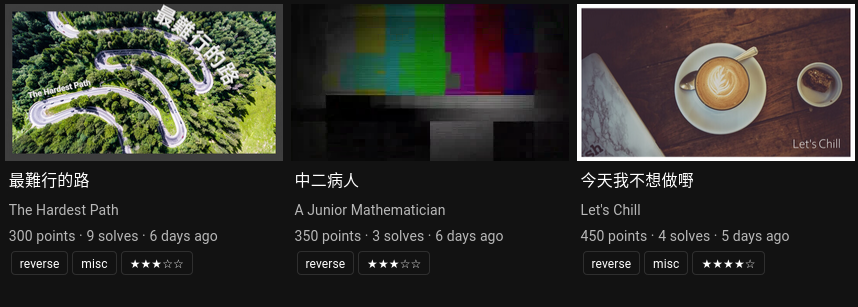
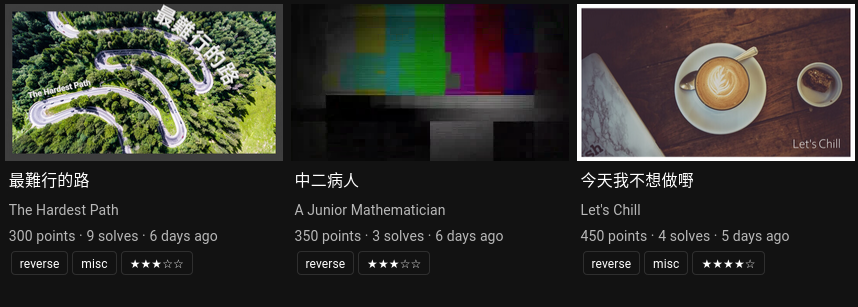
As the third part of the series, three reversing challenges will be included: The Hardest Path, A Junior Mathematician and Let’s Chill.
2021-11-18
:: Mystiz
#ctf
#hkcert-ctf
#challenge-writing
#crypto

In this part, three harder crypto challenges will be covered: Tenet: The Plagarism, Sratslla SEA and Sign in Please, Again.
2021-11-18
:: Mystiz
#ctf
#hkcert-ctf
#challenge-writing
#crypto
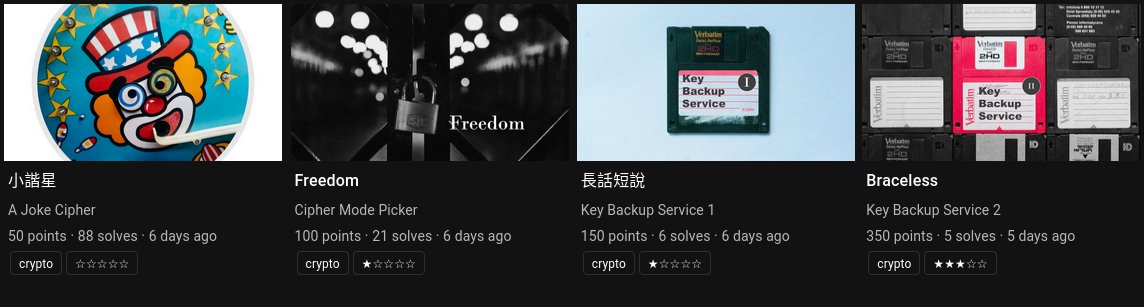
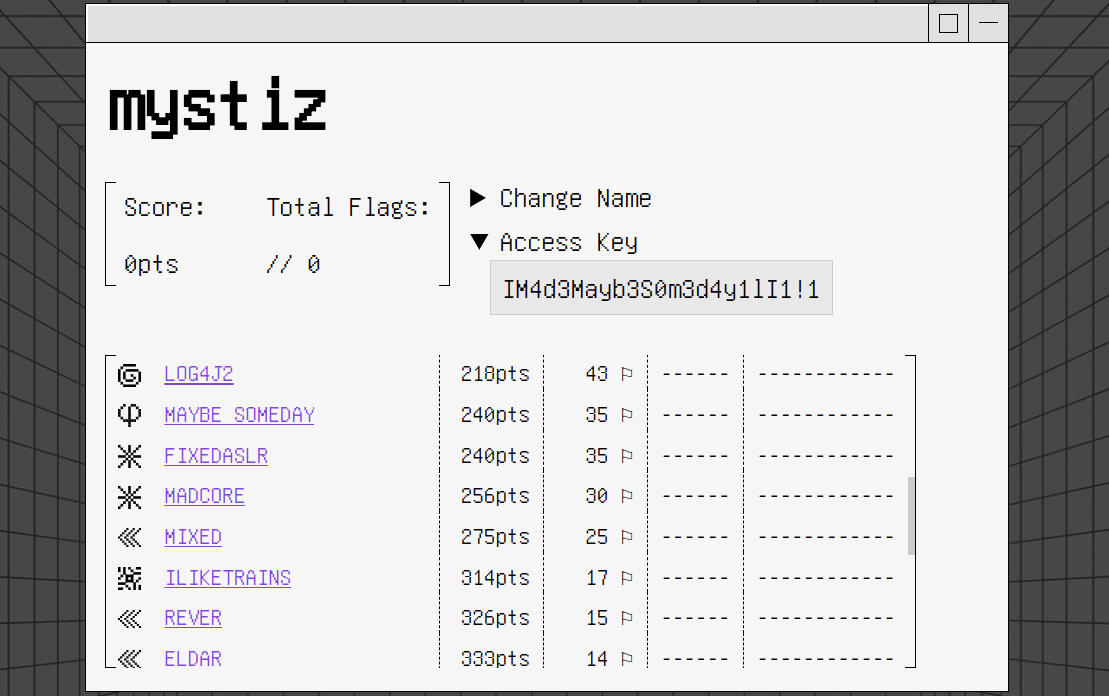
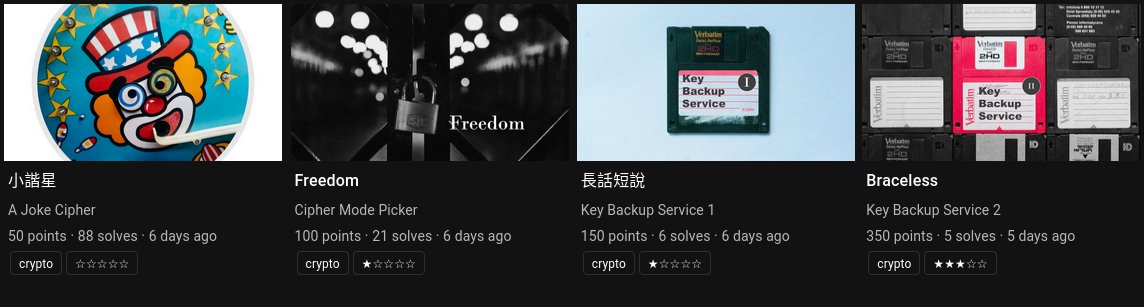
Black Bauhinia coorganized HKCERT CTF 2021 and helped 95% of the technical stuffs, including challenge setting, platform development, infrastructure and etc. I will be writing a series of blog posts talking about the contest, and the first four would be the writeups of the challenges those I wrote.
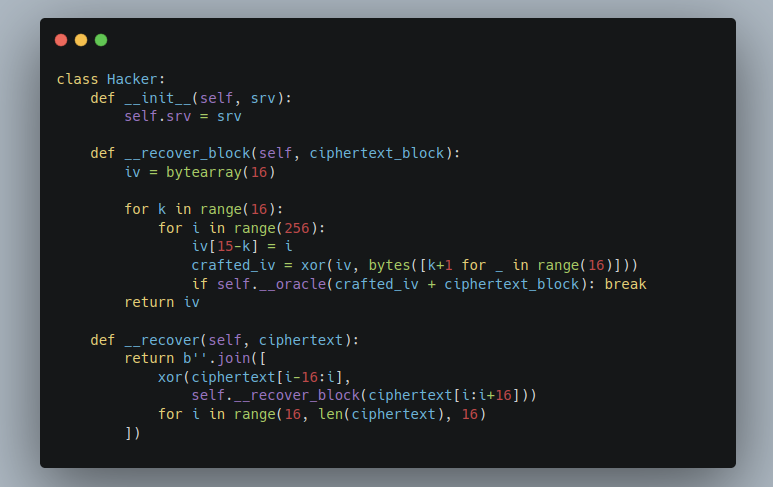
In the first blog post, we will be going through four easier crypto challenges: A Joke Cipher, Cipher Mode Picker, Key Backup Service 1 and Key Backup Service 2.
2021-03-28
:: Mystiz
#ctf
#hkcert-ctf
#challenge-writing
On August 2020, @blackb6a was invited to co-organize HKCERT CTF 2020 (which is held on November 2020) as one of the challenge authors. This is a CTF for secondary and tertiary students in Hong Kong. Although I had experience preparing CTFs earlier, this is actually the first CTF officially prepared by Black Bauhinia. I have written four challenges for this CTF - Sanity Check II (Web), LF2 (Reverse), Sign In Please (Crypto) and Calm Down (Crypto). There will also be some stories behind the scenes.
2021-01-29
:: Mystiz
#ctf
#challenge-writing
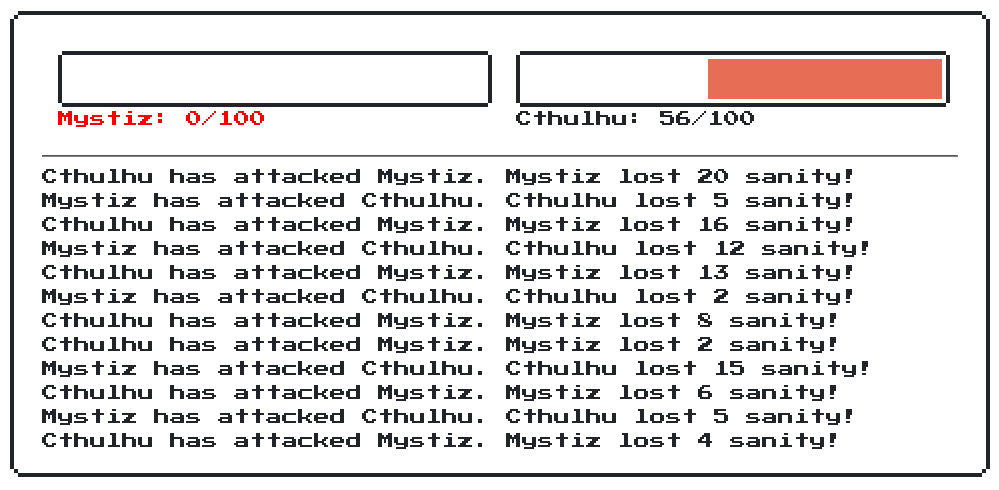
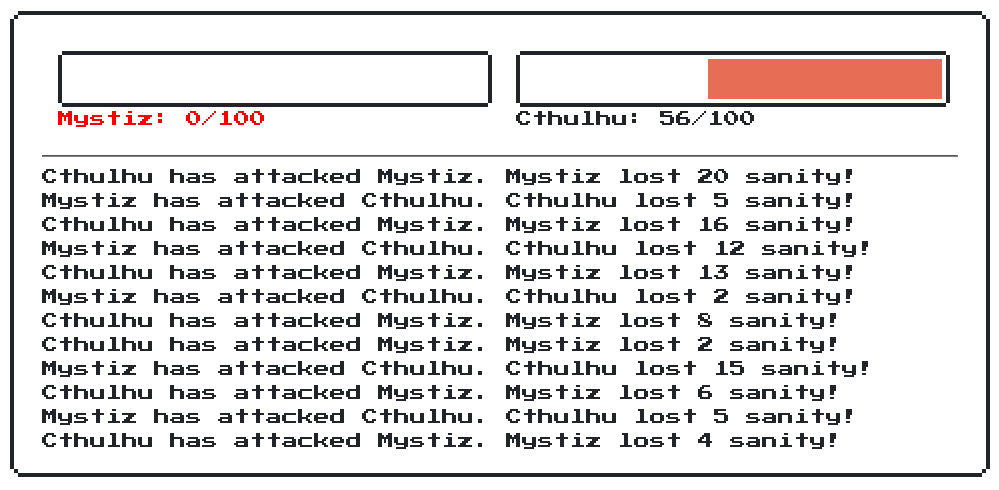
This is a beginning of a new series of blog posts that I review CTF challenges those are not publicly accessible. Generally I will spend some time to solve the challenge while discussing with the author, and give some feedback of the challenge. To kick-start, let’s look at hoifanrd from Firebird CTF team has shared a challenge he created some days ago.
2021-01-18
:: Mystiz
#ctf
#firebird-training
#crypto
#challenge-writing
I have written four question for Firebird Internal CTF - Oofbleck (Crypto), Obvious Transfer (Crypto), RC4 (Misc) and Prooof-ooof-Wooork (Reverse, Misc). I will be including all of them in this blog post.
2020-09-21
:: Mystiz
#ctf
#firebird-training
#crypto
#challenge-writing
Rotten Secured Algorithm is the only challenge that I have written for Firebird Intro CTF. Two people (out of 166) ended up solving the challenge. There is a Python script attached in the challenge, as well as the output file. Let’s see what’s going on in the Python…